

The Covid-19 pandemic accelerated an already increasing trend of remote work popularity and presented businesses with a whole host of new cybersecurity concerns. As the pandemic wains, there has been a lasting desire for companies to continue to offer remote work positions. IT personnel need to combat the equally increasing threat from cybercriminals as well as manage the difficulties of a dispersed workforce. These cybersecurity tips for remote workers can help you focus your employees on security while you focus on how to get repeat business from customers.
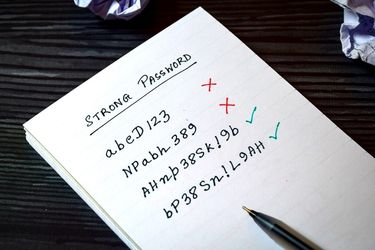
To be frank, most people’s passwords are terrible. One word with a mix of upper and lowercase letters and the occasional special character is child’s play for any bad actor with rudimentary coding skills or the ability to purchase a program on the dark web. Research has shown that a short passphrase including the usual mix of letters, numbers, and symbols is exponentially harder to crack with brute force as well as being less likely to guess. It’s also important to require different passwords for each login that your employees have; that way if one is compromised, it doesn’t provide access to several systems.
Related to passwords, multi-factor authentication involves a secondary method of verifying the identity of the individual logging in above and beyond their password or passphrase. There are a number of authenticator apps readily available for free, and there are other options such as sending a text message, phone call, or email containing a unique code that must be entered.
All of these complex passwords can become a hassle to handle, and the rule of thumb is that the more difficult a process is to complete, the more likely people are to find ways to bypass or skip the said process. To avoid that, a password vault can securely store your employees’ passwords behind biometric security features, and many of them allow the user to copy and paste login credentials to speed up the process as well.
If you offer a hybrid work environment, it’s much safer to issue company-owned phones, laptops, tablets, and other devices to your employees who will be working remotely. This allows your IT staff to ensure that updates are routinely installed, antivirus software is up to date, and it limits the potential for device compromise through personal use as your employees should be using their own devices for those activities.
Even small businesses would see a major benefit to issuing devices over the potential negative financial, civil, regulatory, and reputational damage of a data breach. This is especially true if your company handles sensitive data. If you intend to allow employees to bring their own devices, you should consider implementing policies that include regular installation of software updates, current antivirus subscriptions, active firewalls, and verification of the same by your IT staff.

You should write into your remote work policy that public wifi networks are not to be used under any circumstances. If your employees will be traveling or working outside of their homes, then providing them with a personal hotspot is an easy way to ensure that they are accessing a secure and uncompromised network, and it effectively negates the simplest forms of the man in the middle attack.
At least during the initial onboarding process, your employees should consent to IT security personnel remotely accessing their home network. This is to verify that their router and network are configured properly and appropriately secured. Firewalls should be in place and a strong password with no less than WPA2-PSK encryption. If they are handling sensitive data or accessing secure networks on which sensitive data is hosted, then WPA3 encryption should be mandated. You want to do everything you can to prevent cyber criminals’ attempts to gain access to poorly secured or unsecured home wifi networks and therefore breaching your own systems.

Far and away, the weakest link in your business’s cybersecurity posture is your employees. The human element is the single biggest factor that can defeat millions of dollars in equipment and security measures by simply not using them as directed or falling victim to social engineering scams. Phishing, spear-phishing, smishing, whaling, and other similar frauds are perpetrated by exploiting trusting individuals and tricking them into disclosing login information through various means.
Whether it’s random text messages, emails, or phone calls seeking information by pretending to be a potential client or a targeted attack on accounting or purchasing personnel exploiting a time-sensitive transaction with wiring instructions, these types of scams have a fairly high rate of success with very minimal cost and an equally low degree of risk for the cybercriminals. Providing continuing training to your employees on recognizing and avoiding these scams as well as basic information security tactics should become a part of your culture.
At E-Marketing Associates, our goal is to help small businesses grow. We know that it’s hard to compete with the big guys who have seemingly unlimited budgets, so we offer a wide range of small business marketing products that can help you compete. Whether you’re looking for more leads, search engine optimization, website design, or even reputation management, reach out to see how we can help.
Weak passwords are easily cracked with automated tools. A strong, unique passphrase that mixes words, numbers, and symbols is far harder to brute force or guess, reducing the chance that criminals gain entry to company systems.
Multi-factor authentication adds a second verification step, such as a phone code or authenticator app, after the password. Even if a password is stolen, attackers still need that extra factor, dramatically lowering the risk of unauthorized access.
Company-issued devices let IT control updates, firewalls, and antivirus, keeping systems consistent and secure. Personal devices often lack these safeguards and may be used for risky activities, increasing the chance of malware or data leaks.
Public WiFi is easily monitored or spoofed by attackers. Remote workers should avoid it and instead use a personal hotspot or trusted home network with WPA2 or WPA3 encryption to keep data private.
Regular social engineering training teaches employees to spot phishing emails, fake texts, and urgent phone scams. Understanding warning signs and verification steps helps prevent credential leaks that could bypass even the best technical defenses.